APIsec Ping Identity SSO Configuration
Overview
This document outlines the process for deploying the APIsec SaaS application to the Ping Identity application with SAML authentication, with two groups configured for access control.
Prerequisites
- Ping Identity tenant with administrative access
- APIsec login with “ADMIN” user role
1. Implementation Steps
-
Open Ping Identity
-
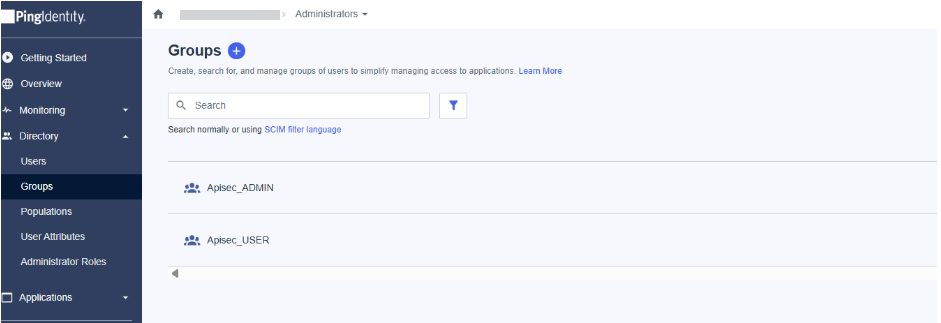
Navigate to the Directory > Groups
-
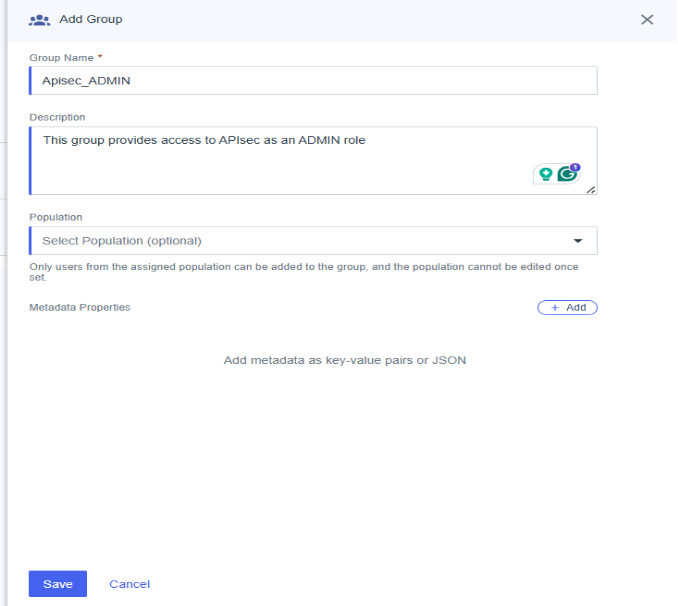
Create a new group by clicking the Plus button next to Groups and add the two groups Admin and User and save.
1.Create the first security group for the APIsec application USER role
-
Group name: APISEC_USER
-
Group description: This group provides access to APIsec as a USER role
2.Create a second security group for the APIsec application ADMIN role
-
Group name: APISEC_ADMIN
-
Group description: This group provides access to APIsec as an ADMIN role
-
2. Application Registration
-
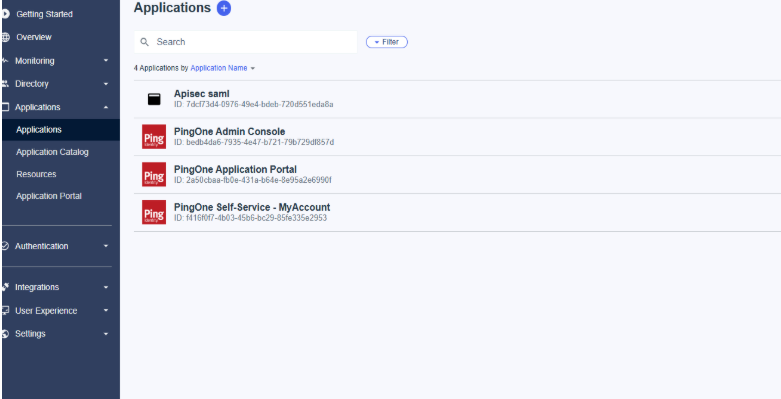
In the left navigation panel, click "Applications".
-
Add New Application
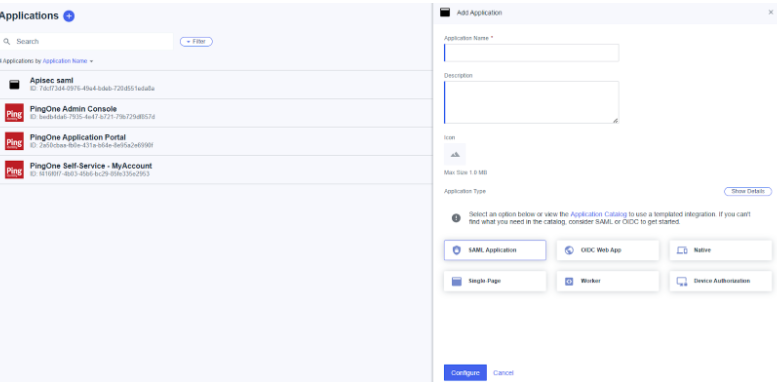
Add the Application name, and choose the SAML Application under application type. And click Configure.
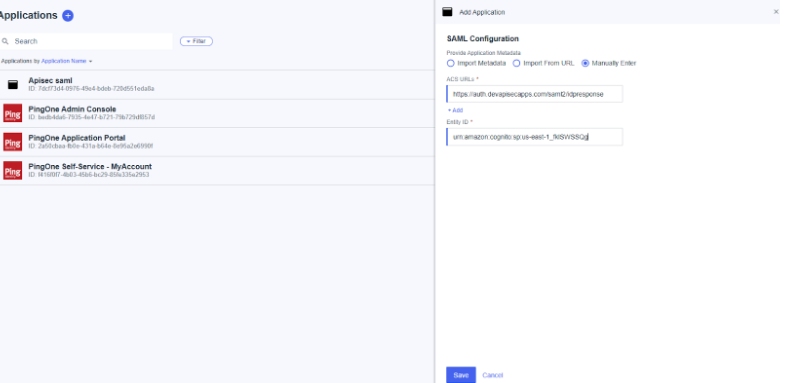
On the next page, provide the application metadata by selecting Enter manually.
Enter the ACS URL and entity ID.
These values are available in the APIsec platform under 'Setup Single Sign On' and by selecting Ping Identity.
3. Update the configuration
-
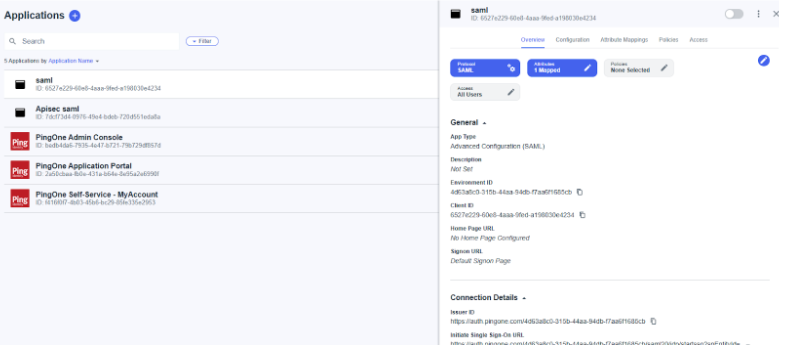
Now open the SAML application which was created.
-
Navigate to the configuration and click edit from the top right. And update the Select Name ID format by selecting the emailAddress one and click save.
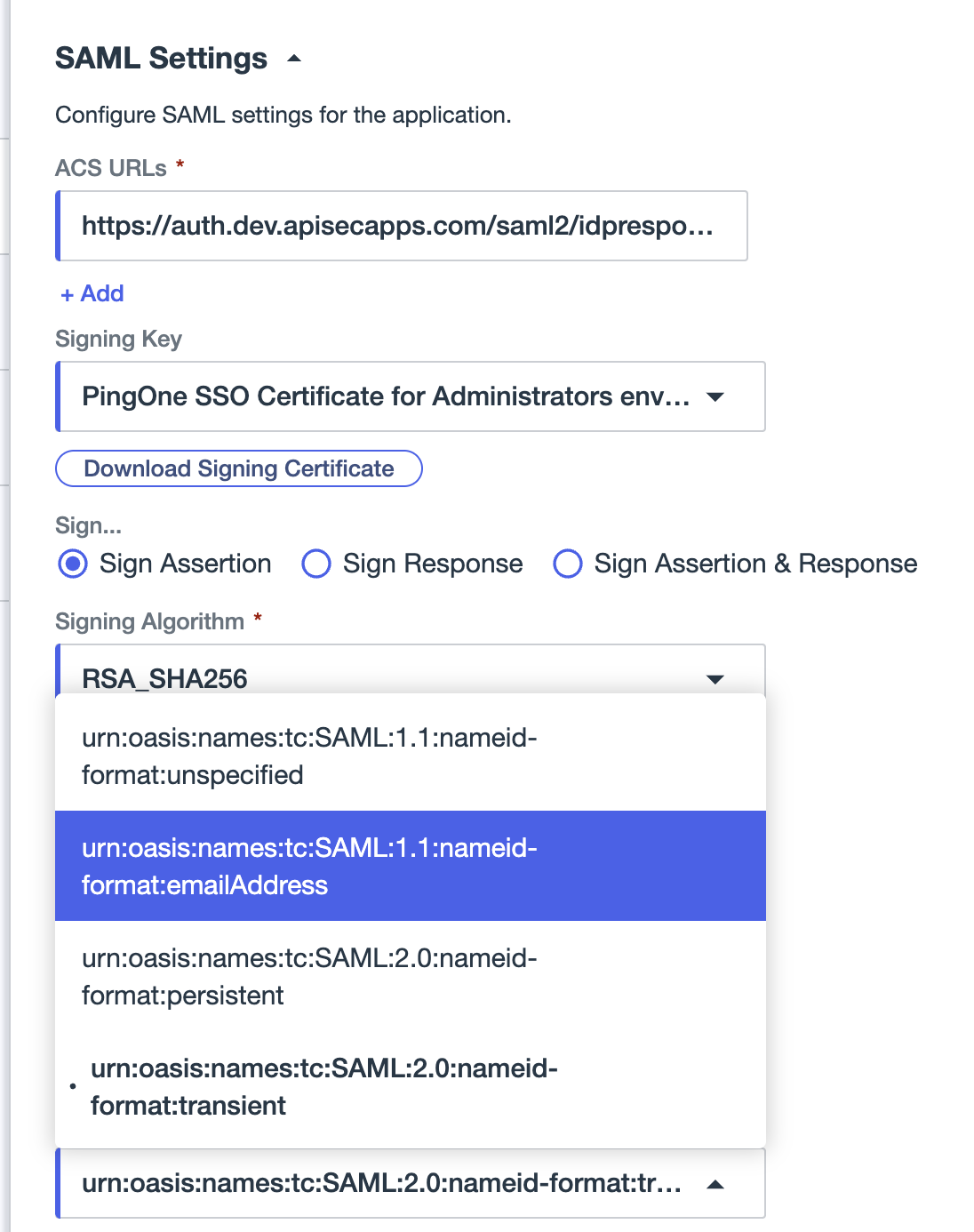
-
Navigate to Attribute Mappings, and enter the APIsec attributes and its corresponding values from the PingOne, as below, and save.
Add the Apisec SAML attribute and map to PingOne as below:
APIsec SAML Claim PingOne Mapping http://schemas.xmlsoap.org/ws/2005/05/identity/claims/apisecrolesGroup Names http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddressUsername http://schemas.xmlsoap.org/ws/2005/05/identity/claims/displayNameGiven Name 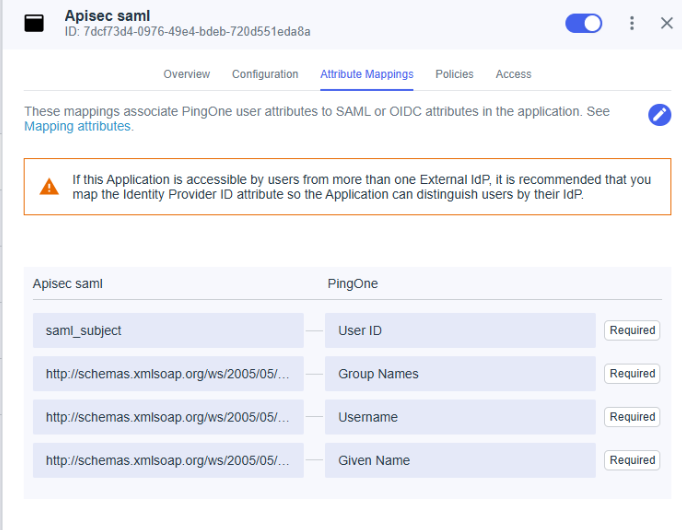
-
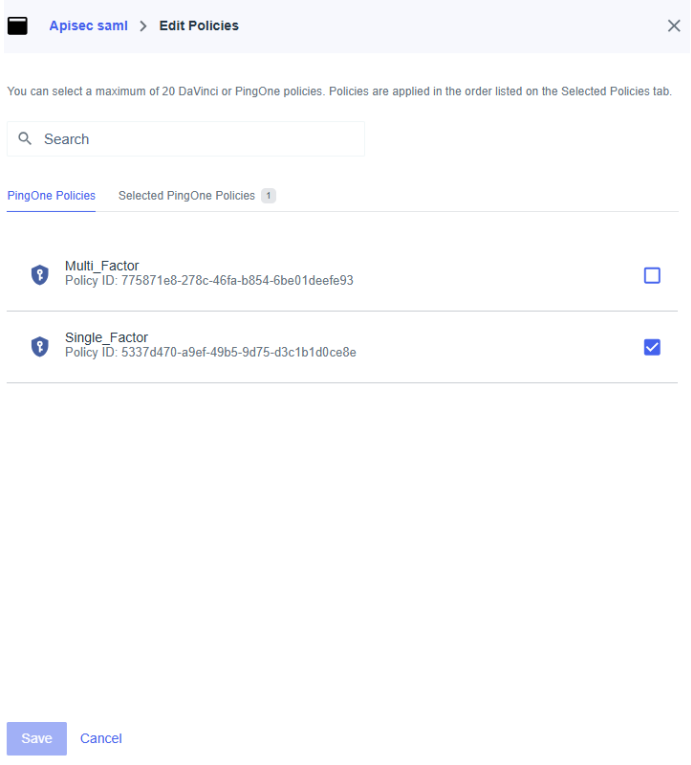
Navigate to Policies and select the Single_Factor and save.
-
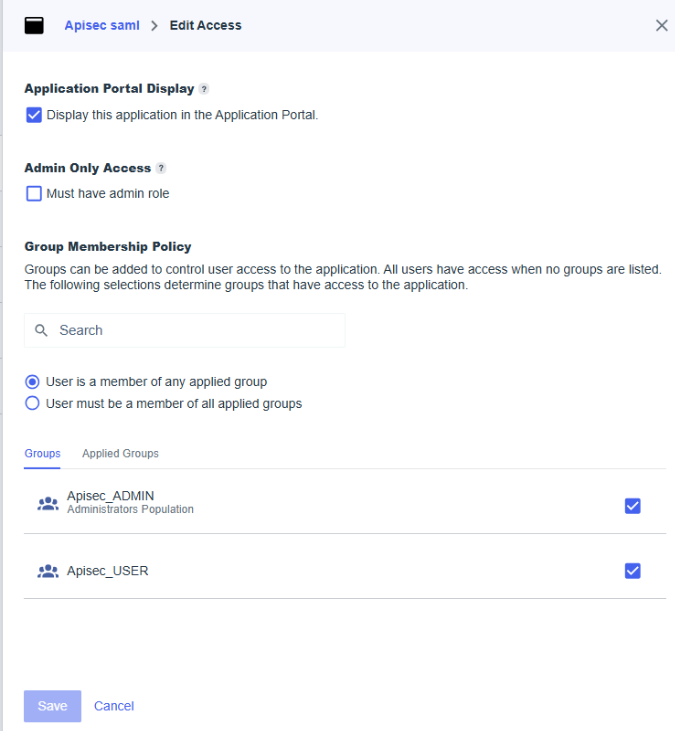
Navigate to Access and select the Group Membership Policy and save.